Identifying and securing internet-facing resources is an essential part of cloud security risk management. Google Cloud offers tools to help you understand risks and add strong access controls to your organization and projects where they are needed. These tools and controls can help mitigate the risks such as the recent critical security vulnerability (CVE-2024-3094) discovered in the XZ Utils compression software.
This vulnerability affects sshd, a popular tool for secure remote access, and could allow attackers to execute remote code on servers without requiring authentication. While Google Cloud Compute Engine customers who rely on our supported public images are not affected by this vulnerability, those using custom images should refer to our security bulletin for remediation guidance.
This vulnerability highlights the risks of Internet-exposed cloud resources, and presents an opportunity to strengthen your security posture and implement best practices for such resources. Two Google Cloud security tools that can help are Identity-Aware Proxy (IAP) and Security Command Center (SCC):
Prioritize and mitigate risk with Google’s cloud-first security controls.
How IAP can shield against SSH attacks
IAP offers a critical first layer of defense for internet-facing resources such as apps and virtual machines. IAP can enforce authorization based on the following signals:
-
User context: Ensure only authorized user groups gain access.
-
Device context: Mandate that access devices meet specific criteria such as corporate-managed, with disk encryption, and using a specific operating system version (or above) in order to approve access. It also offers advanced posture controls with certificate-based access using mTLS.
-
Network context: Limit access based on IP address, ranges, and geolocations.
As a Google-managed service, IAP offers a simpler and robust alternative to traditional SSH authentication services.
IAP can help prevent unauthorized access to internet-facing resources by:
-
Blocking unauthorized access: IAP blocks any attempt to connect to a protected service without strong authentication and authorization. IAP would proactively block exploit attempts from unauthorized users or devices by enforcing strong context-aware authorization, requiring elements like managed (trusted) devices, certificate-based mTLS, and other attributes. These protected resources can reside in Google Cloud, other cloud environments, or even on-premises.
-
Removing public IP addresses: IAP eliminates the need for Internet-facing IP addresses on your virtual machines. This reduces the attack surface, making those machines harder to find in the first place.
Wayfair, a major player in the U.S. retail space, has implemented IAP to enhance their cloud security posture. They rely on IAP’s device posture checks to ensure only a specific set of employees using approved corporate devices with strict security standards can access their sensitive Google Cloud resources.
IAP can add a powerful and proactive layer of defense to help mitigate potential future attacks — including SSH attacks — by enforcing context-aware authorization and minimizing the attack surface.
Understanding and prioritizing risk with Security Command Center's Risk Engine
Not all vulnerabilities pose the same level of risk. The XZ Utils vulnerability is a good example of a vulnerability whose impact depends on how you’ve set up your cloud environment.
Security Command Center's Risk Engine can help add valuable context to vulnerabilities, prioritizing risks based on their potential to compromise your high-value assets if exploited. It does this through attack path simulation.
Let's imagine the Risk Engine analyzes a scenario where a compute instance with the XZ Utils vulnerability is publicly exposed. The engine could proactively determine if this is a high-risk attack path by analyzing:
-
Initial access: Attackers could exploit the XZ vulnerability to gain unauthorized SSH access to the instance.
-
Lateral movement: Misconfigurations could allow attackers to move to other systems within the project.
-
High-value target: Attackers could reach a database containing sensitive customer data and exfiltrate it.
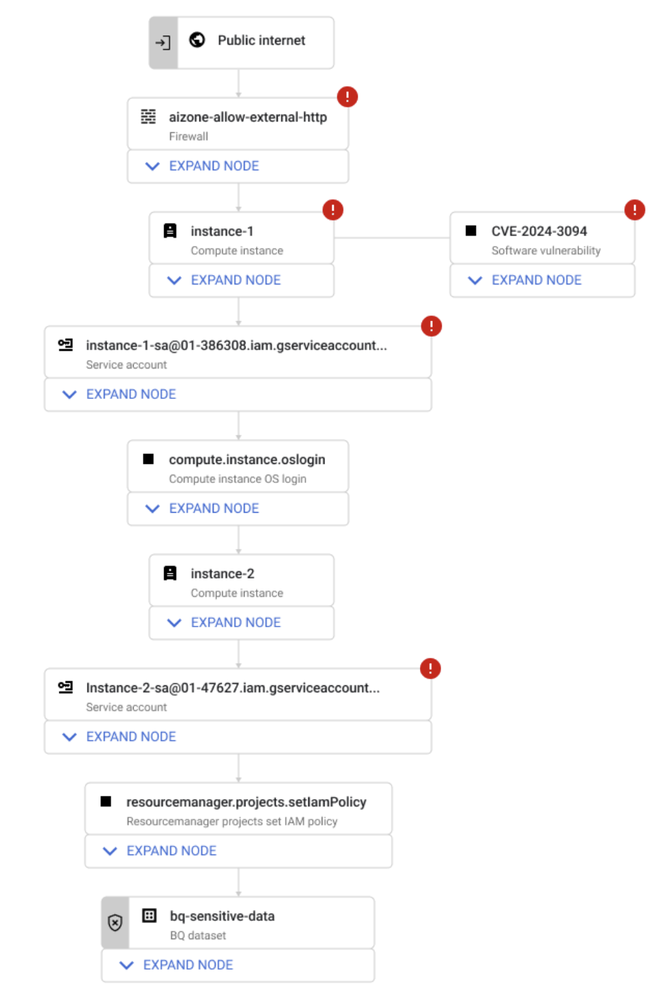
SCC Risk Engine’s contextual analysis to identify and prioritize risk.
The high level of risk exposure revealed by this contextual analysis highlights the urgent need to patch the vulnerability, strengthen SSH access controls, and review the permissions of a potentially compromised instance, which can help you prevent the attack scenario before it happens.
Learn more about IAP and SCC
You can learn more about getting started with IAP from our how-to guides. We also offer guidance on secure SSH/RDP administrative access using IAP and secure access to web applications hosted on Google Compute Engine using IAP.
You can learn more about SCC from our product demo video, and the latest on the Risk Engine in this video and from this presentation at Google Cloud Next.
 8 months ago
67
8 months ago
67